If someone knows the correct "tag" to use instead of file length, i could just plug it into other script I have and get the same list of EFS files instead of Zero Length files. End of problem. 
-questorfla
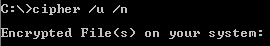
Or just use the cipher command: cipher /U /N >encryptedfiles.txt
If you don't have encryption enabled it'll just bomb out:

Otherwise (I don't have any encrypted files but you get the idea):
I wouldn't be surprised if it required all the encryption keys for every user on the system to be able to detect encrypted files belonging to each user.
You could also probably use Powershell to recurse a tree looking at the extended file attributes, (which is where the encryption attribute hides - the only way to see it from DOS is the
fsutil usn readdata command).
Addendum: There's some methods shown on the following page:
A Fast Way to Find EFS Folders and FilesIncluding a VB Script and the
EFSInfo command off the Server 2003 CD.
Addendum2: And a Powershell script from
TechNet:
get-childitem c:\ -Recurse -Force -ErrorAction SilentlyContinue | Where-Object {$_.Attributes -ge "Encrypted"} | format-list fullname, attributes

 Recent Posts
Recent Posts



