SUPPORT PROJECT:
HELP AND ASSISTANCE:
Lots of clever free utilitiesThe Donation Coder site is offering hundreds of free utilities all full-featured with no nag screens. They use a novel licensing system: you have to register to get a free license key which allows you to download any number of programs on the site. This key lasts six months after which you must return to the site to download another free license key. After a year you are given a permanent license. Alternatively, you can make a once-up donation of any size and get a permanent key straight away. It's a clever and ethical way to encourage users to recognize the work done by freeware authors and I support it fully. The quality of the utility programs offered is very high and a number are unique in what they do. Highly recommended.
Lots of clever free utilitiesThe Donation Coder site is offering hundreds of free utilities all full-featured with no nag screens. They use a novel licensing system: you have to register to get a free license key which allows you to download any number of programs on the site. This key lasts six months after which you must return to the site to download another free license key. After a year you are given a permanent license. Alternatively, you can make a once-up donation of any size and get a permanent key straight away. It's a clever and ethical way to encourage users to recognize the work done by freeware authors and I support it fully. The quality of the utility programs offered is very high and a number are unique in what they do. Highly recommended.
Mircryption is a security addon for a variety of irc clients (primarily mIRC) that encrypts your conversations for secure private communication.
It is an open source project that was first hosted in December 2001 on the SourceForge website (original SourceForge webpage is still online here).
While mircryption originally began as a single .dll (written in C++) and mIRC script, it now consists of a suite of tools that supports several other clients (including xchat), as well as the psybnc irc bouncer and the eggdrop irc bot program, and provides a wide range of functions.
- Channel text, Private query windows, DCC Chats, Actions, Topics can all be encrypted.
- No need to modify the way you work - text is encrypted and decrypted automatically; encryption status of conversations is clear but unobtrusive.
- All crypto-related algorithms used are taken from published, common, trusted sources.
- Encryption algorithm is Blowfish (no known vulnerabilities); encryption keys are themselves stored in encrypted form.
- User-friendly key management routines; menu driven and easy to temporarily disable & re-enable encryption on a channel, send plain text quicky, etc.
- Source code is C++ (with MS visual studio project / makefile for xchat) and a 150k mirc script.
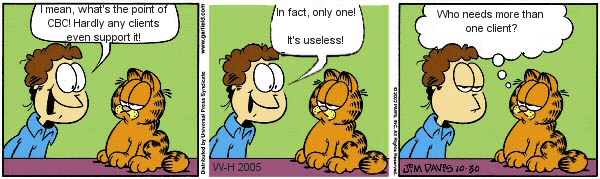
- Supports CBC mode encryption.
- XChat plugin version runs on a wide variety of unix / linux / macosx machines (http://www.xchat.org/).
- You can browse the online help pages for the mircryption addon: here.
- The mircryption discussion form is: here.
- Main Downloads
- Addons and Extras
- Compatible Clients and Code
- History and Change Log
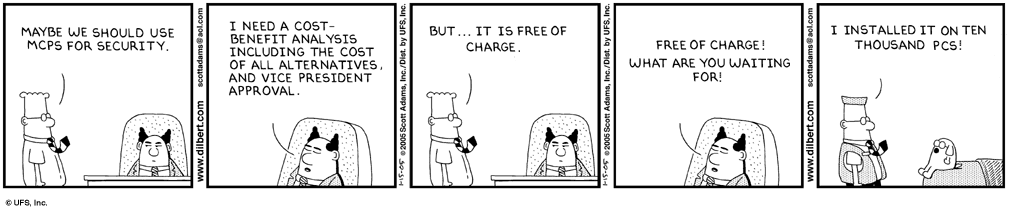
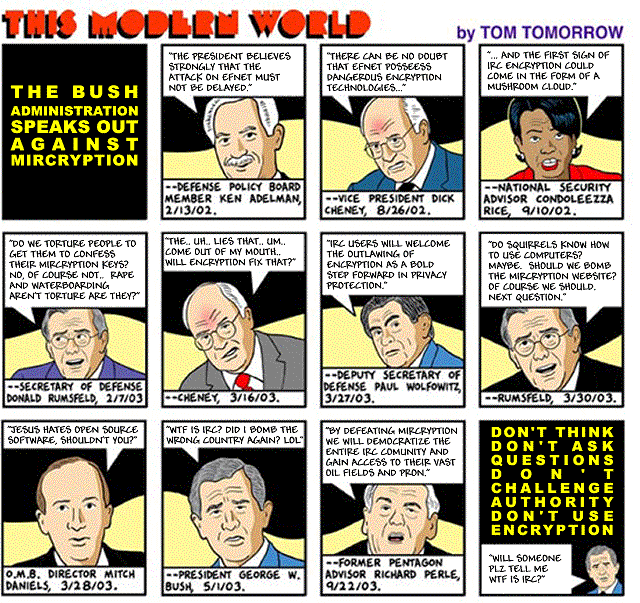
- Comics and Humor
- Related Pages
- CBC Encryption Algorihm
- Credits
- Main Downloads
- Addons and Extras
- Compatible Clients and Code
- History and Change Log
- Comics and Humor
- Related Pages
- CBC Encryption Algorihm
- Credits
Main Downloads
- Mircryption Core Zip v1.20.01 - Mar 7, 2011 - The core mircryption script and dll (mIrc users need only this).
- Mircryption Extras Zip v1.20.01 - Mar 7, 2011 - Includes source code and extra scripts and optional stuff.
- Mircryption XChat2 Addon - Github source code repository (maintained by Gregor Jehle).
Addons and Extras
Mircryption Board
- The newsboard stores blowfish encoded text only. It has no decryption code, it simply serves as a repository for transfering mircryption(blowfish) messages between users. No keys are ever kept on the eggdrop shell, which means no assumptions are made about the integrity of the shell hosting the news bot.
- Supports unlimited number of user-defined sections for organizing posts, with independent permissions for setting who can add/delete posts and create new sections, etc.
- Can record topic histories in a given section.
- News administration program can run on an eggdrop through a tcl script or as a local mirc script run by a user who is consistently connected to the server.
- Source code is standard C++, tiny tcl wrapper for eggdrop, 60k mirc script for client.
- News server runs on any shell eggdrop; client runs on MS Windows only.
- Included as part of the mircryption extras zip pacakage download.
Mircryption PGP
- Two levels of safety: choose between maximum convenience and maximum security.
- Invulnerable to man-in-the-middle attack when used with trusted independent pgp keys (level two).
- Automatically authenticate your pgp identy over irc, or send small files through irc.
- All transmissions occur through the irc server and irc proxies/bnc - ips are never revealed.
- Uses standard pgp keyrings - compatible with your existing pgp keys and you can use all pgp features, keyservers, etc.
- Requires an installation of Pgp 6.5x or greater (note: PGP source code is avail. on the net).
- Employs Counterpane Lab's Yarrow PRNG.
- Source code is Borland C++ Builder, and 18k mirc script.
- For MS Windows only (not available for xchat/unix).
- People mostly prefer to use the FishDH addon to exchange keys, but Mpgp is still available for the security conscious.
- MPgp seems to suffer from occassional crashing, and is being phased-out in favor of a new key exchange system to be implemented in the next version of mircryption.
- Included as part of the mircryption extras zip pacakage download.
Mircryption Web Updater
- No automatic checking - you tell it when to check for updates.
- Nothing done behind your back - no phone home, no information uploaded to web site.
- Describes changes between your installed version and latest web version.
- You choose which files to update, can be interrupted at any time. Nice progress display.
- Keeps backups of all replaced files.
- Support for using a web(http) proxy.
- Code is a 45k mirc script (MS Windows use only)
- Included as part of the mircryption extras zip pacakage download.
Mircryption Encrypted Log Viewer
- Works with both encrypted logs and normal non-encrypted logs.
- Search all log files for multiple strings at the same time - get a summary of # of occurences in each file.
- Keywords are highlighted in the current log being viewed; easy search within the current log file.
- Re-encrypt plaintext logs or remove encryption from encrypted logs; commandline use for batch operations.
- Url highlighting and double-click to launch.
- Quick-launch from within mircryption.
- Sort by date, name, size, search hits.
- Source code is Borland C++ Builder.
- For MS Windows only (not available for xchat/unix).
- Included as part of the mircryption extras zip pacakage download.
McpsFishDH
- This key exchange script is compatible with fish and mircryption (and supports mircryption cbc mode if both users are running mircryption).
- NOTE: this dll is not made by us, so we cannot vouch for its security - use at your own risk (it is open source though). Mpgp is more secure but is much more difficult to use.
- Included as part of both the mircryption core and extras zip pacakage downloads.
Other Small Scripts
- koncool ([email protected]) has made a great page of mirc scripts that he has mircryptified: http://anti-me.org/koncool (site down currently).
- hadez wrote a tiny perl script for the xchat version of mircryption that can be used to automatically set your mircryption passphrase on startup: here.
Compatible Clients and Code
XChat Addon
- Mircryption XChat2 addon - Github source code repository (maintained by Gregor Jehle).
Irssi Addon
- Download the Mircryption Irssi addon, mainted by Gothic. Discuss on our forum here.
Other mircryption-compatible protocol support
- The Fish addon (not written by us) is compatible with mircryption and is available for mirc, xchat, and irssi.
- The open source KVirc client (free open source) has recently added support for mircryption-compatible encryption/decryption, and it even supports the new cbc modes. It is cross platform for Linux, Mac, Windows, FreeBSD.
- The open souce, cross-platform java jIRCii client now supports mircryption/fish, thanks to butane (jIRCii coder) and k2r (java mircryption coder).
- The first mircryption/fish compatible handheld phone/pda irc implementation is now available for symbian/uiq smartphones: Quirc.
- New *nix irc client adding support for mircryption/fish: Konversation.
- The XIrc IRC client for MAC OSX -- now supports mircryption (for Mac also see xchat and kvirc above).
Mircryptified Psybnc
- Important: Tunning psybnc on a remote pc and using encryption is a SEVERE security risk(!), and you will be exposing your encryption keys to anyone who can sniff traffic or access the computer running the psybnc if you do not use this properly.
- You should only be using psybnc encryption if you are running psybnc on the same computer as your client or on a lan computer (which will allow you to use it to mircryption-enable any irc client), or if you are using SSL to connect to your psybnc.
- Included as part of the mircryption extras zip pacakage download.
Mircryptified EggDrop (McEggdrop)
- Please remember that giving your eggdrop bot the key used on a channel can be a huge security risk if you don't run your own shell, because it means the shell owner will be able to examine your eggdrop files and determine your channel key.
- Special thanks to those that helped with McEggdrop (heidel, bounty, slask, stdragon, and #egghelp channel, esp. Pixelz and slim).
- Updated 11/17/07 by heidel
- Included as part of the mircryption extras zip pacakage download.
Other Language Code
- JAVA - A Java class for encryption/decrypting mircryption/blow/fish compatible text has been written by some generous java coders; it can be downloaded here: mcpsBlowfishJava.zip [updated jan 9, 2006].
- PHP - Php code to encrypt and decrypt had been implemented in the new and exciting php::irc project (local download of sample code here: phpirc.zip, check funs.php).
- C# - Markus Jevring wrote some C# code to show how to interface with the mircryption.dll and perform encryption and decryption; download here: mcpsCSharp.zip.
- VB.NET - BlkSmth adapted the C# code and created vb.net code to interface with the mircryption.dll and perform encryption and decryption; download here: VB.net-CryptoWrapper.zip.
- PERL - A Perl mod for encrypting/decrypting has been written by Max and generously made available here: Crypt-ircBlowfish-1.0.zip. A Perl script for irssi encrypting/decrypting based on the above code but adding support for advanced cbc mode has been written by Gothi[c] and generously made available here: blowssi. This code would be *very* useful for anyone wishing to implement cbc mode and you can find a longer discussion of some of the tricks to getting it to work on the dc forum here.
- Delphi - godfucked adapted the Perl code above and an existing blowfish component to produce native delphi code to perform encryption and decryption; download here: ircBlowFish-Delphi.zip.
- Ruby - an anonymous person adapted the Perl code above to produce ruby code for encryption and decryption: MircryptionFishForRuby.zip.
- OTHERS - If you want help porting the legacy ECB encryption algorithms to another language, the major difficulty is the use of a non-standard base64 function. Come to #mircryption on efnet for help, and check the C++ source code for Fish (which has a cleaner implementation of the strange base64 code than mircryption does), or the Php, Perl, or Java ports above.
History and Change Log
March 7, 2011
Mircryption 1.20.01 - Democracy Revolution Edition. This is just a zip repackaging of the previous version of mircryption, suitable for install in the new Mirc 7 and on Windows Vista/7 machines; we are moving away from using setup installers from here on out.
August 08 2008
irssi plugin released. At long last an irssi script/plugin has been released which can do mircryption (and fish) compatible encryption/decryption, and even supports the more secure mircryption CBC mode. Written by John Sennesael (Gothi[c]). Discuss on the dc forum here.
November 17 2007
Heidel fixes for tcleggdrop_mcpsfuncs have been posted: Fixes: fixed putmsg/putnotc - no longer suppressing error messages from triggered bind procs and invalid put commands. Correctly handling options in put commands (e.g. putserv "test" -next). For more info and download visit the mircryption eggdrop page.
August 20 2007
Mircryption/XChat Unofficial Early Release Page. Gregor Jehle has been doing great working tweaking the XChat port of mircryption, and he's created a nice page where he will now be maintaining the latest unofficial Mircryption/XChat version.
April 09 2007
Mircryption 1.19.01 Released. Mirc Win32 - added variable to disable space-to-160 conversions (set %mc_multispacefix to no). Mirc Win32 - fixed minor bug on line 2654 referencing $ename should have been %ename - thanks Cham. Mirc Win32 - now %mc_uniqueserverkeys = yes will ADD network prefixes to ensure uniqueness between servers when using mirc multiserve. Mirc Win32 - added ability to explicitly alias or dealias channel names, just set %mc_cnamealias_#CHANNAME #CHANNAMEALIAS. Mirc Win32 - nick tracking is now disabled by default. Mirc XChat - updated the xchat source version with some major improvements by gjehle to fix action bug, color highlighting bug, and other stuff(Gregor Jehle) (see this thread)
September 30 2006
McEggdrop Eggdrop Functions Updated. v1.00.29. # updated 07/19/05 by bounty - added new cbc encryption code to mceggdrop, using existing tcl cbc libraries. [bounty's cbc_functions integrated into to mcegdrop by mouser]. # updated 11/27/05 by heidel - fixed trigger count for mc binds table (visible through .mcbinds partyline command). # updated 02/20/06 by mouser - improved (but not tested yet) ability to prevent text from being encrypted if prefixed with ' or NOCRYPT. # updated 08/27/06 by heidel - fixed esay and emsg for eggdrop 1.6.18
January 27 2006
Serious Security Bug - All Users Should Update. This is the first time in 4+ years that we've had reason to release a security update for mircryption. Today (1/27/06) we were alerted by the people at RainbowCrack-Online that they had discovered a buffer overflow risk in the mircryption dll, which could be demonstrated by a program called ircfuzz by Ilja van Sprundel. Ircfuzz generates and floods a mirc client with huge amounts of random data, and it turns out that mircryption does not sufficiently protect itself from the possibility of abnormally long channel names or nick names(>255 characters). While it is not possible for a normal user to trigger such an attack, it is still possible that a malicious server owner could send commands that could crash your irc client while running mircryption, or possibly exploit the buffer overflow in order to execute malicious code. While we know of no existing exploit of this bug in the wild, this should be considerd a SERIOUS risk, and all mircryption users should update immediately. Both the mircryption.mrc script and mircryption.dll files as of version 1.15.00 have been redundantly fixed to protect against flaw. You can update using the online updater, or by installing the new version over your old version, or by manually downloading and replaceing the new mircryption.dll and mircryption.mrc files on the download page. Thank you to rainbow-crack-online for alerting us to this bug.
January 23 2005
More Code for Other Languages. New submissions of code to perform fish+mircryption compatible encryption+decryption from Delphi and Ruby.
January 09 2005
Update of Java Mircryption Script. Minor update of k2r's micryption compatible blowfish routines.
August 15 2005
New Symbian/Uiq Phone(Pda) Irc Client. The first mircryption/fish compatible handheld phone/pda irc implementation is now available for symbian/uiq smartphones: Quirc (donate!).
July 18 2005
tcleggdrop_mcpsfuncs (mceggdrop) Updated to v1.00.26. Heidel has brought us fixes and new functions, including the long-asked-for esay+emsg commands from the telnet partyline to make your eggdrop speak encrypted. He also brings us a huge new version of the mckey.tcl bonus script (originally coded by slask and now extensively improved and documented by heidel) for setting mceggdrop eggdrop keys from the partyline and using a botnet. While still considered in beta testing, this script may be invaluable for you botnet and partyline people.
June 27 2005
Mircryption Packages Updated to v1.11.27. The Full Suite and Lite version setup pacakges available on the main download page have now been updated to the latest versions; see the online help or update file on the beta download page for full information. No major features or security risks have been added since the last package, but tons of little fixes.
April 15 2005
McPsybnc Updated to v2.3.2-5. The mircryptified version of psybnc (mcpsybc) with support for fish/mircryption (and the new cbc encryption) has been updated to match the latest psybnc 2.3.2-5.
April 10 2005
New Web Pages. New web pages on DonationCoder.com are being updated.
April 01 2005
Java IRC Client Supports Mircryption. The open souce, cross-platform java jIRCii client now supports mircryption/fish, thanks to butane (jIRCii coder) and k2r (java mircryption coder).
March 25 2005
Mircryption Cartoon Contest Ends! The First Annual Mircryption Cartoon Contest has ended. Visit the mircrypted humour page to see the submissions.
March 23 2005
AntiVir False Positive on stdio.dll. We got a report that the AntiVir antivirus program was giving a false positive virus alert on stdio.dll inside the Suite download of Mircryption. It's not a virus. You don't need stdio.dll for normal use of mircryption so if you are paranoid about it just unpack the setup exe manually using winzip and delete the file. Details about stdio.dll can be found in its directory in the download.
February 15 2005
PlaintextBlocker.tcl. An early beta of a new tcl script to be used with mcegddrop encrypted eggdrop script is now available in the mceggdrop zip download linked below; it will let you specify commands you want to block use of in plaintext.
February 12 2005
Tutorial Links. The tutorial links have been upgraded with M.D.Ferrante's fantastic tutorials that walk new users through the entire process of installing, loading, and using mircryption for the first time(!).
January 17 2005
KVirc Irc client adds support for blow/fish/mircryption Encryption. The very nice open source KVirc irc client has added support for encrypting and decrypting compatibly with mircryption/blow/fish. It even supports the new cbc mode! KVirc works on both windows and *nix (the new code is in the cvs release now and will make its way into official snapshots soon).
January 15 2005
Java Mircryption Routines. Due to the dilligent work of several java coders, there is now a java class that can be used to encrypt and decrypt mircryption/blow/fish text. This was a non-trivial task due to oddities in java treatment of text and the non-standard base64 routines. See Extra Downloads section.
January 15 2005
Mircryptified Psybnc. We modified the latest psybnc (2.3.42) to support mircryption (and fish/blow), including the new cbc encryption keys. Just prefix keys with 'mcps;' or /cbc;'. By running this psybnc on your local pc, you can make any irc client compatible with mircryption (!). Read more in the Extra Downloads section.
January 10 2005
Major New Feature: Blowfish CBC Mode. We finally decided that the increased security of CBC mode encryption was too valuable to be postponed until version 2.. Simply use the prefix 'cbc:' in front of your key value to employ CBC mode for a specific window/channel. You can read more about using the new CBC mode here.
Feb 08 2003
New Download Packages - Mircryption is now packaged as an installer to make it easier for new users and upgraders. However, you do *NOT* have to use the setup program if you do not want to. Since the installer executables are are zip-compatible, you can unpack them manually with any unzip program (even the unix unzip command) if you prefer.
Jan 23 2003
Linux / BSD / MacOSX Support is HERE! - at the bottom of this page you can download the first sneak beta release of the xchat 1.9x compatible mircryption plugin(!). Beta testers please report experiences on the mircryption forum.
Comics and Humor
Submissions to the 2005 Mircryption Humor Contest



c_and_f_squirrel_1 - mp3 audio file
candf_are_watched_by_the_nsa - mp3 audio file
candfdoextremedownloading.mp3 - mp3 audio file
Related Pages
Related Projects and Websites
- Mirc Fish 10 - enhanced Fish plugin that supports CBC
- Old Mircryption Forum on SourceForge
- New Mircryption Forum
- Mircryption on #efnet
- Mirc Homepage
- XChat Homepage
- mIRC.Crypt
- cryptoIrc
- purenoise
- klaatu's mIRC Crypto
- gaim-e
- psybnc
- pgp
- counterpane labs
- InvisibleNet
- Fish addon with DH excahnge
- mirccrypt
- php::irc
- jIRCii client
- KVirc client
- egghelp.org - great page with eggdrop scrips and forum
CBC Encryption Algorihm
Mircrytion Support for CBC Mode
Mircryption has recently added support for a new more secure encryption mode, CBC (Cipher Block Chaining) mode.
Summary
To use the new mircryption to use CBC mode, use the prefix 'cbc:' when specifying the key for a channel or window.
Discussion
By default, mircryption uses the Blowfish encryption algorithm in what is known as ECB (Electronic Code Book) mode. ECB mode treats each group of 8 characters as an independent encryption block; and an 8 character block will always encrypt to same the cipher text given a specific encryption key. ECB is considered less secure than other modes, such as CBC (Cipher Block Chaining) mode, but mircryption uses ECB mode by default in order to be compatible with existing encryption addons for mirc.
ECB mode can be considered a risk in certain cases, because it could potentially allow an attacker to build up a dictionary of certain plaintext / ciphertext pairs. A so-called known/chosen text attack can be very risky if the attacker can convince you to encrypt a large amount of text for which they know/choose the original text. On irc, this probably is not a huge risk, because it would be difficult for an attacker to build such a dictionary.
However, the Encrypted Logging feature of mircryption is an example of a situation where a single key might be used to encrypt both public and private channels, and because you might be logging public channels, an attacker could use public logs in comparison with your encrypted version of these logs to build a large dictionary, and then use this dictionary to attack your private encrypted logs.
One way to protect against such an attacj is to use Blowfish in CBC mode.
In CBC mode, a unique (random,sequential,etc.) value is used to start each encrypted string, and each block of encrypted bytes is affected by the previous block. This makes it impossible to construct a dictionary of plaintext-ciphertext pairs. It means, for example, that even if someone can compare the encrypted and plaintext versions of a certain public log file, it will not help them to be able to decrypt other logs encrypted with the same key. Even if you type the same sentence, it will appear differently each time, due to the random initial block.
Recommendation
CBC is considered in all aspects more secure than ECB mode, and we encourage you to use CBC mode in mircryption whenever backward compatibility is not a requirement. The only downside to using CBC mode is that you will not be able to use it when conversing with people who use addons that support only the old Blowfish ECB mode.
Usage
A complete redesign has been planned for mircryption for quite a while, which would introduce an entirely new code base and support for arbitrary plugin algorithms, text compression, message authentification, etc. Until this new version is ready, we are only making minor modifications to mircryption.
However, we decided that for security reasons, support for CBC mode should not be put off any longer.
In order to support this new CBC encryption mode without introducing additional complexity in the user interface, we have employed a very simple technique. If you prefix a key with 'cbc:' then everything after the : is taken as the key, and CBC mode is used with that key.
For example, in channel #mircryption, we might use set the keyphrase for the channel to 'test' while in channel #mircryption2 we might use the keyphrase 'cbc:test'. In the first case, the backward compatible original Blowfish ecb mode will be used with encryption key 'test'. In the second case, in channel #mircryption2, Blowfish will be run in CBC mode, with the encryption key 'test'. Note that the 'cbc:' prefix is not part of the actual encryption key used, but you must specify it when setting the key in order to tell mircryption to use CBC mode in that channel/window.
You can also use the 'cbc:' prefix for setting keys for encrypted logging, as long as your encrypted log viewer has also been upgraded to support CBC mode. We will be modifying the fish dh exchange routine to support CBC mode soon.
Important Notes
If a person with an old version of mircryption or with another irc encryption addon that does *not* support CBC mode sets a key with a 'cbc:' prefix, you will not be able to understand each other. The new version of mircryption will try to alert you to this fact (but uers with older versions will not receive an error message). If you want to check if your output is being encrypted in CBC mode, you can turn on debugging in mirc and type the same sentence twice and examine the encrypted output; if it's the same both times then you are not in CBC mode, if it's different then you are.
Using CBC Mode with Other Tools
Eggdrops (and the mceggdrop tcl addon) do not currently support the new CBC mode keys but the new simple mcps commandline utility does. If you wish to write functions to encrypt and decrypt the new CBC style strings from a language such as perl, php, java, etc., be aware that the new CBC mode routines now use the standard base64 encoding and decoding, and that the first 8 bytes of the encrypted text is the IV block that should be fed to the encryption routine. Additionally, a '*' character needs to be prefixed to the text after it has been encrypted and base64'd (and removed prior to decryption), in order to clearly identify it as being encrypted using CBC mode and facilitate error detection.
Credit
The implementation of blowfish for CBC mode is from http://www.thecodeproject.com/cpp/blowfish.asp by George Anescu. The base64 code used is from 'The Secure Programming Cookbook for C and C++', By John Viega, Matt Messier. Precompiled versions for MacOsX are possible thanks to the awesome open source PearPc emulator.
Credits
Credits and Thanks
The various mircryption programs and scripts include substantial work by various authors.
The main coder for mircryption is mouser ([email protected]). This code is all licensed as open source under the zlib open source lincense, which basically says you can use it for whatever you want as long as you give clear credit. Some other code (including the actual crypto algorithms) may be licensed differently; see below for more information.
The Blowfish algorithm (standard blowfish-448) is used to encrypt all traffic and to encrypt the master keyfile. Blowfish uses a single (symmetric) encryption decription key which must be shared between the parties who are talking.
The blowfish encryption/decryption routines and some dll support functions were orginally taken from Gustavo Picon's mirc blowfish dll source code; there is not much of Gustavo's original dll code left here, but it was Gustavo's dll project that started this project (www.aircscript.com). The dll itself actually just wraps blowfish routines written by Bruce Schneier (author of the famous Applied Cryptography book) and Jim Conger. It is jim conger's actual unmodified c++ source code from the counterpane website that is used in mircryption.
As of version 1.11.02 (January 10, 2005), a new implementation of Blowfish and Base64 encoding has been added to mircryption for use with cbc mode keys (the original implementation is still used for ecb mode). The implementation of Blowfish for CBC mode is from http://www.thecodeproject.com/cpp/blowfish.asp by George Anescu; the base64 code used is from 'The Secure Programming Cookbook for C and C++', By John Viega, Matt Messier.
The MircryptionPgp component uses phil zimmerman's pgp libraries and public-key encryption to securely exchange keys, and the Yarrow pseudo-random-number generator (Bruce Schneier and John Kelsey) to generate random channel keys.
Most of the hard work done by the MircryptionPgp component is done by the free PGP DLL libraries. PGP was originally developed by Phil Zimmerman (http://www.philzimmermann.com), and later distributed by Network Associates (http://www.pgp.com). Although Network Associates stopped development of PGP, in August of 2002 the newly formed PGP Corporation announced that development of PGP would continue under new management. PGP is also maintained at mit (http://web.mit.edu/network/pgp.html) which is a good place to look for more information. Additional downloads can be found at the international pgp home page (http://www.pgpi.org). Source code and binaries for pgp is available on these sites.
The MircryptionPgp addon was written using Borland C++ Builder 5; Michael in der Wiesche's excellent and comprehensive delphi wrappers for the pgp dlls were essential (http://home.t-online.de/home/idw.doc/PGPcomp.htm). Source code for the delphi wrappers is available on that site.
To generate cryptographically secure random channel keys with the MircryptionPgp component, Counterpane Lab's Yarrow was used (http://www.counterpane.com/yarrow.html). This is a well-respected prng developed by Bruce Schneier and John Kelsey. Source code and binaries for yarrow are available on that site.
The mircryption script includes encrypted logging functions which are based on '(advanced logging) v1.0' by ash ([email protected]). The original dll skeleton code was based on work by tabo (http://www.aircscript.com). some c++ coding in xchat port by xro and hadez. Some mirc code for the mcupdater script was adapted from 'Downloader v1.0' by |nsane (www.mircscripts.org). A small function was adapted from 'Multi-Kreate Directory' by zack^ (www.mircscripts.org). Koncool has provided much help mircryptifying other mirc scripts.
The eggdrop scripts were possible with generous help from several pro tcl scripters, most notably stdragon from egghelp.org and from the #egghelp channel on efnet, Pixelz and slim.
We have made use of the wonderful Diffie-Hellman key exchange dll written by the author of the Fish addon.
Many people in #mircryption have contributed substantially to this project, but in providing addon utilities and porting mircryption to other languages, but also just by provided useful suggestions and invaluable testing, including but not limited to housetier, kd, n2u, PyRoZ, ciro, tretnrez, Yun, M|P, Zinc, champi, TU, louv, and many more. Thanks to those who have helped with the graphics for the site and contributed to the humour page, especially anshar and flowpass for his wonderful squirrel mp3s.
I've probably left people off this list uninentionally - please contact me and let me know or let me know on #mircryption on efnet. Special thanks to Gregor Jehle for lots of work improving the xchat version of mircryption.
Please do not use this software for immoral activities; use it because you're irrationally paranoid about things no one cares about. We believe in karma.

 Donate to author
Donate to author Discuss on forum
Discuss on forum
